Security Essentials 2010 is a rogue anti-spyware program from the same family as Internet Security 2010. This rogue is installed by Trojans that pretend to be a Flash update that is required to view online videos. Instead of actually letting you view the video, though, this Trojan will download and install other malware, including Security Essentials 2010. One of the Trojans that will be installed is C:\WINDOWS\system32\smss32.exe that hijacks your desktop with a security warning, shows pop-ups stating that you are infected, and finally installs Security Essentials 2010 on to your computer.
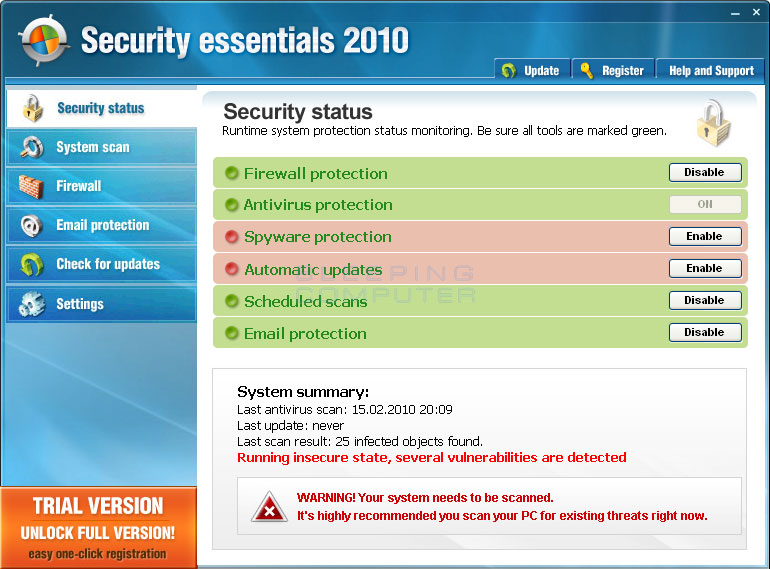
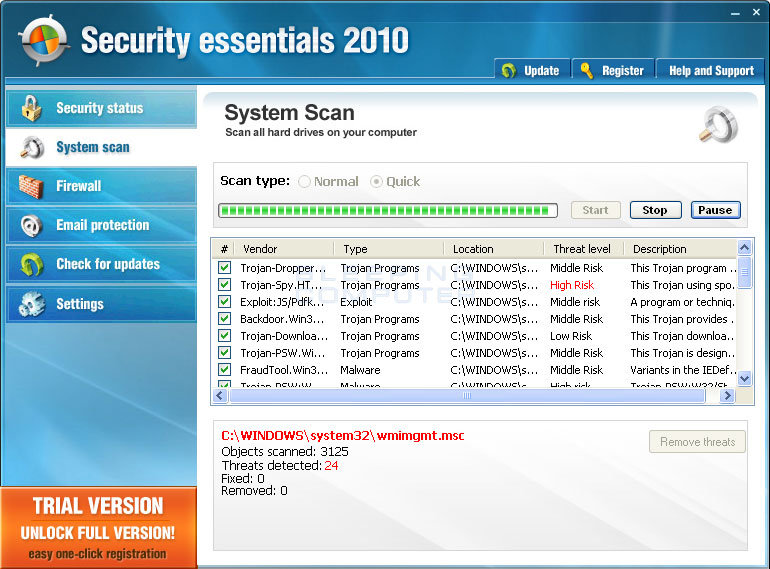
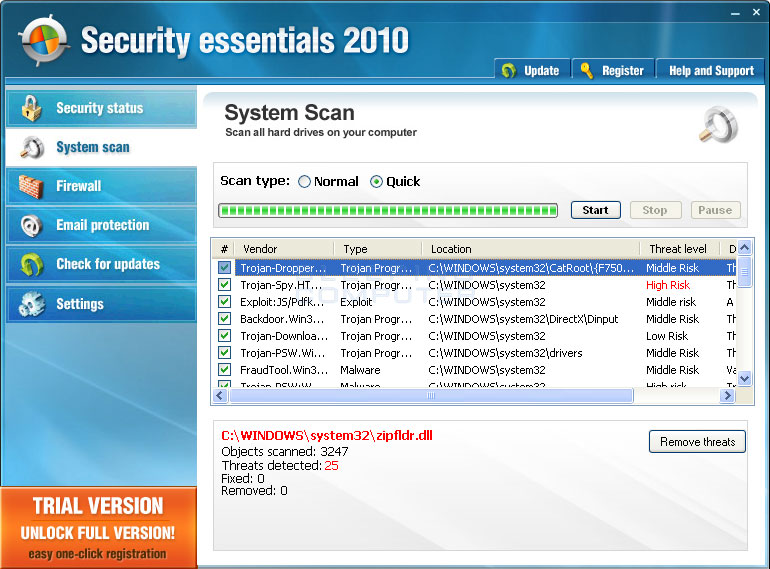
Once Security Essentials 2010 is installed, it will be configured to start automatically when you log into Windows. Once started it will scan your computer, and when done, state that there are numerous infections on your computer. If you try to remove them using this program, though, it will tell you that you first need to purchase it in order to remove anything. As the infections it shows are all fake, and as this program is a scam, you should definitely not purchase it.
While running, Security Essentials will also protect itself by not allowing you to run any executables on your computer. When you attempt to run an executable it will display a message that states the executable is infected and will then terminate the program. The exact message it will show is:
Application cannot be executed. The file is infected. Please activate your antivirus software.
This alert is fake and should be ignored as your programs are not infected. It is only performing this action this so that you cannot launch any programs that will allow you to remove it from your computer.
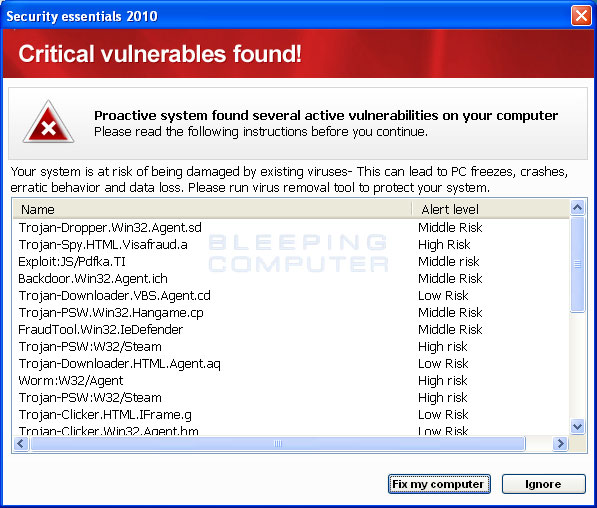
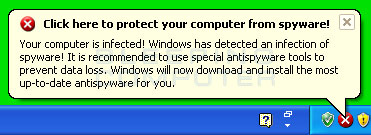
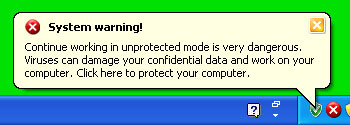
While the program is running you will also see a constant barrage of security alerts appear on your desktop. These alerts may be pop-up windows or little balloon alerts from your Windows taskbar that state active infections have been found, that private and personal data is at risk, or that your computer is under attack. Some of the messages that you may see are:
Your computer is infected! Windows has detected an infection of spyware! It is recommended to use special antispyware tools to prevent data loss. Windows will now download and install the most up-to-date antispyware for you.
Click here to protect your computer from spyware!Attention! System detected a potential hazard (TrojanSPM/LX) on your computer that may infect executable files. You private information and PC safety is at risk. To get rid of unwanted spyware and keep your computer safe you need update your current security software. Click OK to download official intrusion detection system (IDS software)
ERROR
Application Error.The instruction at 0x009a6f9a referenced memory at 0x00000000. The memory could not be written.Click on OK to terminate the program.Security Warning!
Worm.Win32.NetSky detected on your machine.
This virus is distributed via the Internet through e-mail and Active-x objects.
The worm has its own SMTP engine which means it gathers e-mails from your local computer and re-distributes itself.
In worst cases this worm can allow attachers to access your computer, stealing passwords and personal data.
Viruses can damage your confidential data and work on your computer.
Continue working in unprotected mode is very dangerous.System warning!
Continue working in unprotected mode is very dangerous. Viruses can damage your confidential data and work on your computer. Click here to protect your computer.Critical Warning!
Critical System Warning! Your system is probably infected with a version of Trojan-Spy.HTML.Visafraud.a. This may result in website access passwords being stolen from Interner Explorer, Mozilla Firefox, Outlook etc. Click Yes to scan and remove threats. (recommended)
As you can see, Security Essentials 2010 does its best to try and trick you into thinking that your computer has a security problem, when in fact it is the actual infection. Therefore, please do not purchase this program for any reason.
Without a doubt, this program was created to scare you into thinking you are infected so that you will be scammed into purchasing the program. With that said, you should definitely not purchase it, and if you have, you should contact your credit card company and dispute the charges stating that the program is a scam. Finally, to remove Security Essentials 2010 and any related malware please use the removal guide below to remove it for free.
Security Essentials 2010 Removal Options
Self Help Guide
If you are uncomfortable making changes to your computer or following these steps, do not worry! Instead you can get free one-on-one help by asking in the forums.
- Print out these instructions as we may need to close every window that is
open later in the fix.
- It is possible that the infection you are trying to remove will not allow
you to download files on the infected computer. If this is the case, then
you will need to download the files requested in this guide on another computer
and then transfer them to the infected computer. You can transfer the files
via a CD/DVD, external drive, or USB flash drive.
- Before we can do anything we must first end the processes that belong to
Security Essentials 2010
so that it does not interfere with the cleaning procedure. To do this, please
download RKill to your desktop from the following link.
RKill Download Link - (Download page will open in a new tab or browser window.)
When at the download page, click on the Download Now button labeled iExplore.exe download link. When you are prompted where to save it, please save it on your desktop. - Once it is downloaded, double-click on the iExplore.exe
icon in order to automatically attempt to stop any processes associated with
Security Essentials 2010
and other Rogue programs. Please be patient while the program looks for various
malware programs and ends them. When it has finished, the black window will
automatically close and you can continue with the next step. If you get a
message that RKill is an infection, do not be concerned. This message is just
a fake warning given by
Security Essentials 2010
when it terminates programs that may potentially remove it. If you run into
these infections warnings that close RKill, a trick is to leave the warning
on the screen and then run RKill again. By not closing the warning, this typically
will allow you to bypass the malware trying to protect itself so that rkill
can terminate
Security Essentials 2010
. So, please try running RKill until the malware is no longer running. You
will then be able to proceed with the rest of the guide. If you continue
having problems running RKill, you can download the other renamed versions
of RKill from the rkill
download page. All of the files are renamed copies of RKill, which you
can try instead. Please note that the download page will open in a new browser
window or tab.
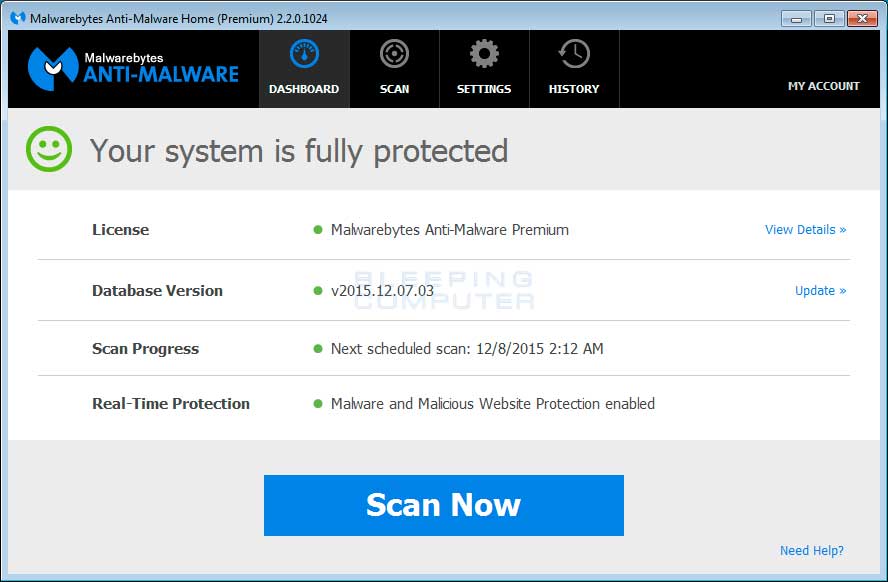
Do not reboot your computer after running RKill as the malware programs will start again. - At this point you should download Malwarebytes Anti-Malware, or MBAM, to scan your computer for any any infections or adware that may be present. Please download Malwarebytes from the following
location and save it to your desktop:
Malwarebytes Anti-Malware Download Link (Download page will open in a new window) - Once downloaded, close all programs and Windows on your computer, including
this one.
- Double-click on the icon on your desktop named mb3-setup-1878.1878-3.0.6.1469.exe.
This will start the installation of MBAM onto your computer.
- When the installation begins, keep following the prompts in order to continue
with the installation process. Do not make any changes to default settings
and when the program has finished installing, make sure you leave Launch
Malwarebytes Anti-Malware checked. Then click on the Finish button. If MalwareBytes prompts you to reboot, please do not do so.
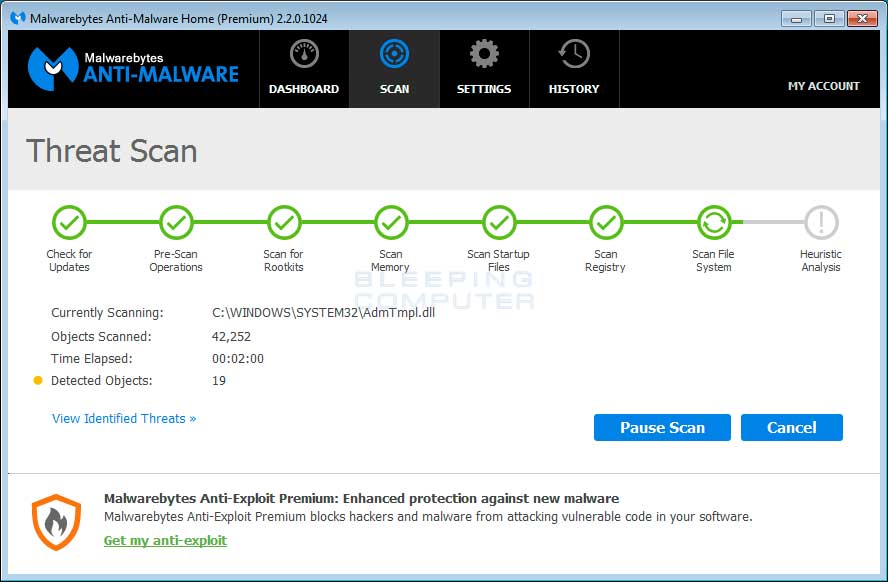
- MBAM will now start and you will be at the main screen as shown below.

Please click on the Scan Now button to start the scan. If there is an update available for Malwarebytes it will automatically download and install it before performing the scan. - MBAM will now start scanning your computer for malware. This process can
take quite a while, so we suggest you do something else and periodically
check on the status of the scan to see when it is finished.

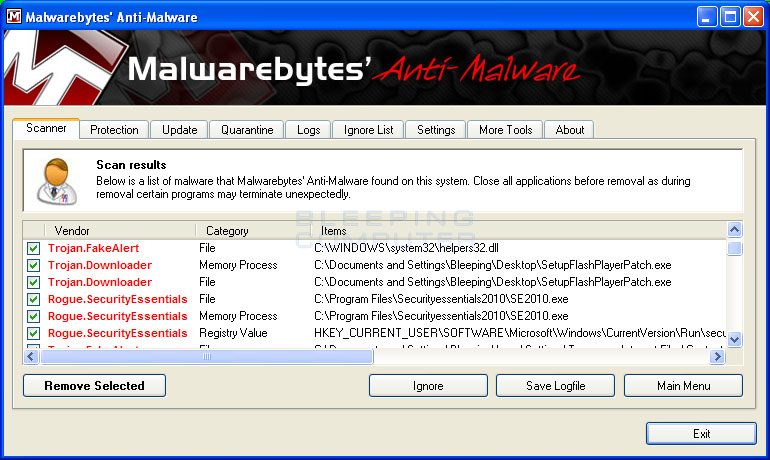
- When MBAM is finished scanning it will display a screen that displays any malware that it has detected. Please note that the infections found may be different
than what is shown in the image below due to the guide being updated for newer versions of MBAM.

You should now click on the Remove Selected button to remove all the seleted malware. MBAM will now delete all of the files and registry keys and add them to the programs quarantine. When removing the files, MBAM may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot, please allow it to do so. Once your computer has rebooted, and you are logged in, please continue with the rest of the steps. - You can now exit the MBAM program.
- As many rogues and other malware are installed through vulnerabilities found
in out-dated and insecure programs, it is strongly suggested that you use
Secunia PSI to scan for vulnerable programs on your computer. A tutorial on
how to use Secunia PSI to scan for vulnerable programs can be found here:
How to detect vulnerable and out-dated programs using Secunia Personal Software Inspector
Your computer should now be free of the Security Essentials 2010 program. If your current anti-virus solution let this infection through, you may want to consider purchasing the PRO version of Malwarebytes Anti-Malware to protect against these types of threats in the future.